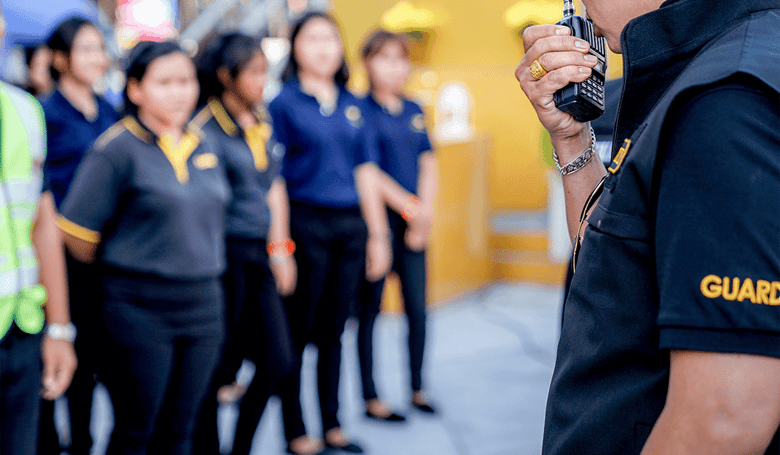
Incident Management
Incident Response Training: Prepare Your Team for the Inevitable
April 19, 2023
2 min read

facility management
Facility Maintenance Management: Best Practices to Boost Productivity
February 15, 2023
2 min read
Incident Management
6 Steps to Creating Your Own Incident Response Plan Template
January 18, 2023
3 min read
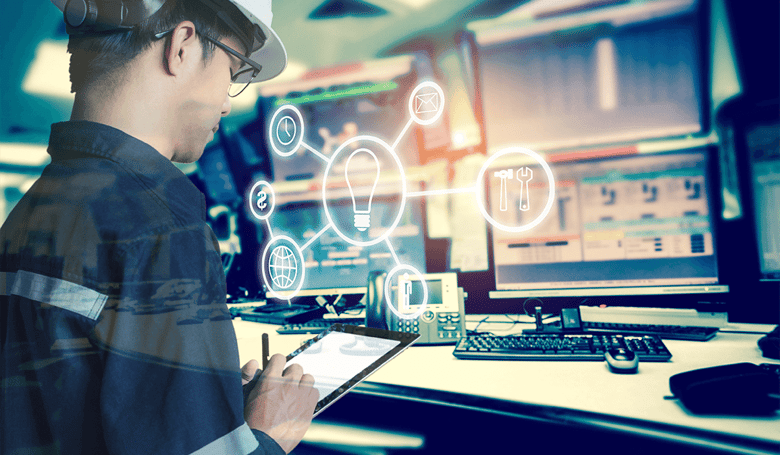
facility management
Facility Management Trends: The Next 10 Years and Beyond
January 10, 2023
4 min read

facility management
Internal Communication System Software for Venue and Facility Management
December 28, 2022
2 min read