Text Communication
How Communications Software Improves Venue Guest Experience Through Better Awareness
November 15, 2022
3 min read

Lost & Found
How Lost & Found Software Improves Guest Experience and Venue Efficiency
November 1, 2022
5 min read

Incident Management
How Mobile Incident Reporting Software Reduces Facility Liability and Drives Efficiency
October 18, 2022
4 min read

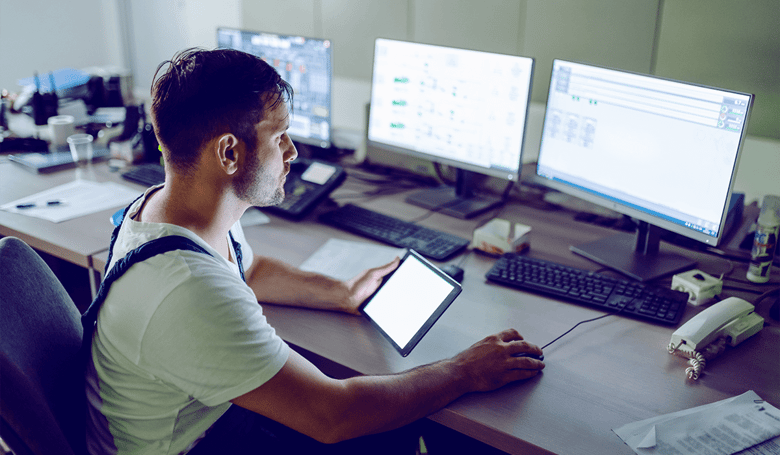
Communication
9 Must-Have Features of Customer Communication Management Software
October 4, 2022
5 min read

Text Communication
5 Ways Mobile Applications Increase Communication for Facility Management and Staff
September 27, 2022
5 min read
Task Management
7 Benefits of Task Management Software for Facility Management
September 20, 2022
5 min read

Lost & Found
Choosing the Right Lost and Found Software for Your Needs
September 13, 2022
5 min read

Lost & Found
How Lost and Found Software Can Salvage a Negative Guest Experience
September 1, 2022
5 min read