“Passwords that took seconds to guess, or were never changed from their factory settings. Cyber vulnerabilities that were known, but never fixed. Those are two common problems plaguing some of the Department of Defense's newest weapons systems, according to the Government Accountability Office,” writes Bill Chappell in their recent NPR article entitled “Cyber Tests Showed 'Nearly All' New Pentagon Weapons Vulnerable To Attack, GAO Says.”
“The flaws are highlighted in a new GAO report, which found the Pentagon is ‘just beginning to grapple’ with the scale of vulnerabilities in its weapons systems,” Chappell explains.
“Drawing data from cybersecurity tests conducted on Department of Defense weapons systems from 2012 to 2017, the report says that by using ‘relatively simple tools and techniques, testers were able to take control of systems and largely operate undetected’ because of basic security vulnerabilities,” the article continues.
According to the NPR piece, “The GAO says the problems were widespread: ‘DOD testers routinely found mission critical cyber vulnerabilities in nearly all weapon systems that were under development.”
Chappell explains in the article that “When weapons program officials were asked about the weaknesses, the GAO says, they ‘believed their systems were secure and discounted some test results as unrealistic."
And that’s why we’re writing today’s article.
We don’t want you to believe anything.
You’ve got to know your ‘systems’ are secure.
Agree?
That’s why it’s critical to identify your flaws now and understand potential vulnerabilities.
But, you’re probably wondering how right?
Well, if you’re “just beginning to get a grapple” of the importance of your operation’s strengths, weaknesses, opportunities for improvement, and outside threats – we’ve got you covered.
Keep reading; we’re going to share why and how a proven methodology is a key to plugging holes in your operation and knowing everything is secure.
Believe us.
The Chosen Methodology for Securing Your Operation
We’ve worked with many experts in various industries to help them improve the efficiency and effectiveness of their operation.
Factors such as weaknesses, vulnerabilities, and security concerns are often addressed and evaluated.
Much like the points made in Chappell’s NPR article.
We even admit; we’re a bit obsessed in our pursuit to understand what’s needed to help you achieve success.
Regardless of your operational function, we’ve always worked to discover ways to contribute to the success of every operational function.
And, we have no plans of stopping any time soon.
We ask these questions, and the exciting thing that happens is we continue to readdress them.
You’ll notice you can ask the following once, twice, ten, 100 or 247 times and the answer may either be the same, change, or have a slight variation of a previous solution.
- What are the fundamental needs of the industry?
- What’s important and relevant to the experts in each field?
- What are the collective strengths and weaknesses that they all share?
- What’s missing?
Nothing ever stays the same.
It can’t.
That’s when we had an epiphany.
Operations across every industry must move away from the reactive mindset they’ve had for years.
It’s time for a proactive approach – one that will evolve with the demands of the environment.
So, we’ve done just that.
And while our long-term relationships with industry experts have shaped Proactive Operations, it’s their participation and contribution that secures the longevity of properties worldwide.
With Proactive Operations and operations management software, you have the advantage of maximizing your performance to ensure you know your operation is secure for years to come.
Go here now to learn how, and then speak with our team to see how you can employ Proactive Operations and maximize your performance using operations management software.
Over to You
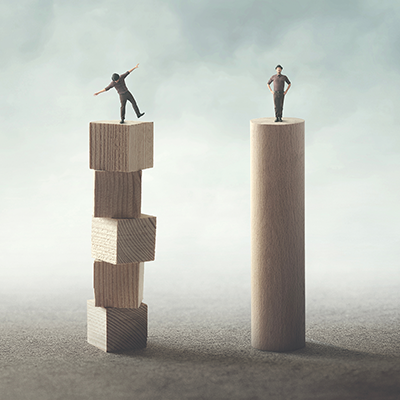
Your operation is a multitude of moving parts. That’s why understanding the potential for threats and identifying your vulnerabilities matters so much.
By using the Proactive Operations methodology, you can grabble the holes in every area of your operation, but also act on the various opportunities that exist.
You need a disciplined approach to managing your team, how they perform, and all the systems you have in place. That way you don’t just believe your operation is secure – you know it is.